Since I recently got more involved in cracking and setup hashcat on my host PC I thought this would be a good time to try this room by Try Hack Me! Lesgeddit.
Task 1
The first task was to crack 5 hashes. I have decided to go with the [RockYou.Txt](https://github-releases.githubusercontent.com/97553311/d4f580f8-6b49-11e7-8f70-7f460f85ab3a?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Credential=AKIAIWNJYAX4CSVEH53A%2F20210221%2Fus-east-1%2Fs3%2Faws4_request&X-Amz-Date=20210221T220418Z&X-Amz-Expires=300&X-Amz-Signature=e1b20c7e026b1bf39a10d1e8611f750c9ef197204b271cf777837148402d0d10&X-Amz-SignedHeaders=host&actor_id=0&key_id=0&repo_id=97553311&response-content-disposition=attachment%3B%20filename%3Drockyou.txt&response-content-type=application%2Foctet-stream) wordlist.
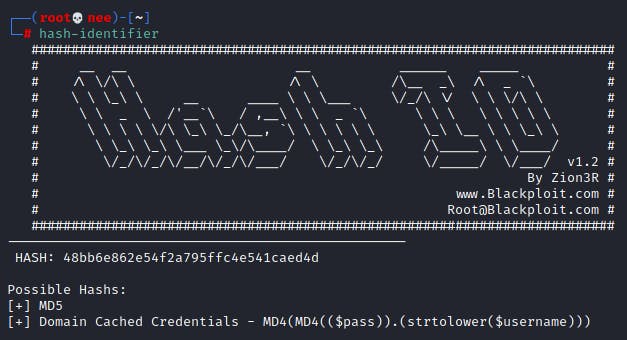
1.1 ~ MD5
48bb6e862e54f2a795ffc4e541caed4d : MD5
Hash Identifier
Hashcat
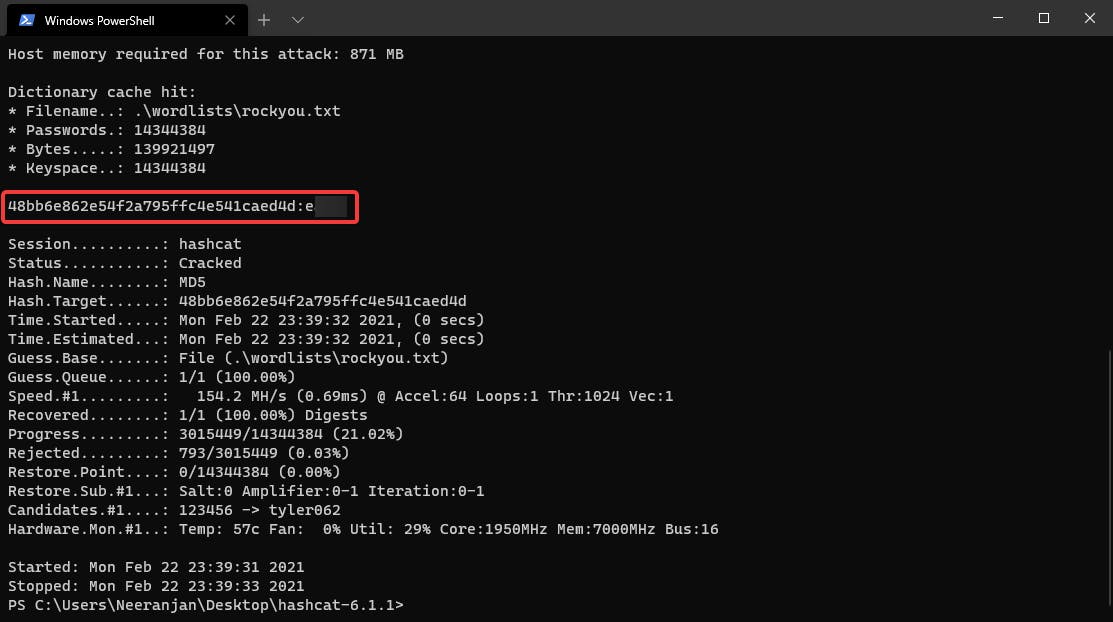
.\hashcat.exe -m 0 .\hashes\hash.txt .\wordlists\rockyou.txt -O --force
1.2 ~ SHA-1
CBFDAC6008F9CAB4083784CBD1874F76618D2A97 : SHA-1
Hash Identifier
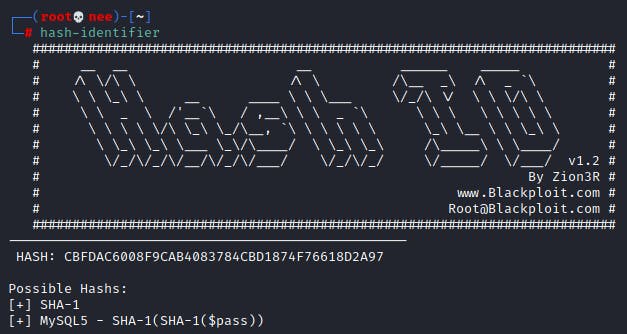
Hashcat
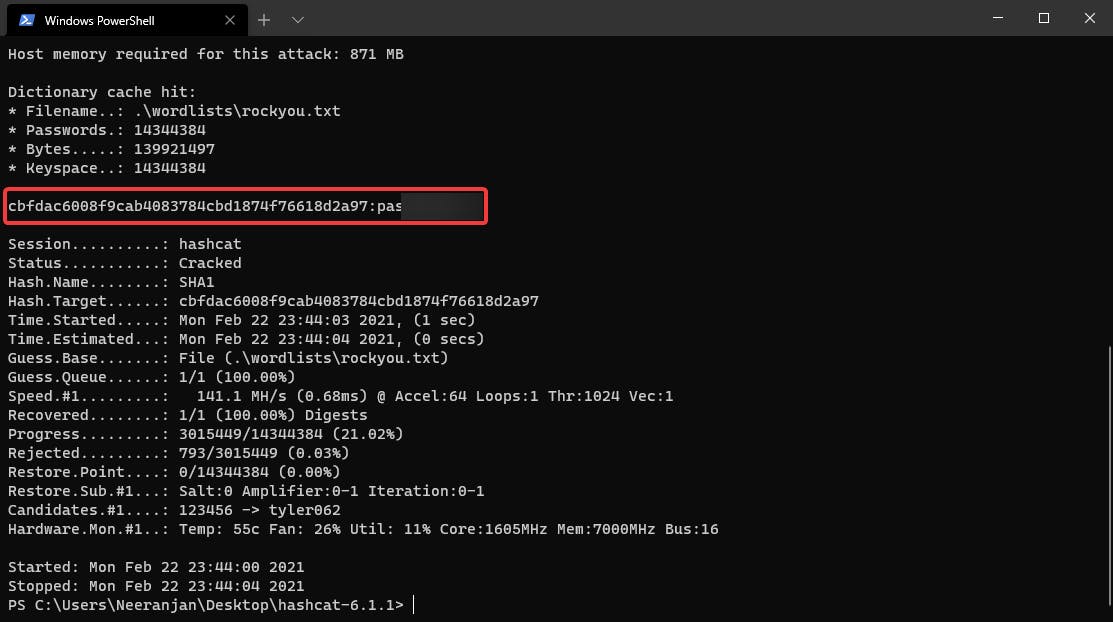
.\hashcat.exe -m 100 .\hashes\hash.txt .\wordlists\rockyou.txt -O --force
1.3 ~ SHA-256
1C8BFE8F801D79745C4631D09FFF36C82AA37FC4CCE4FC946683D7B336B63032 : SHA-256
Hash Identifier
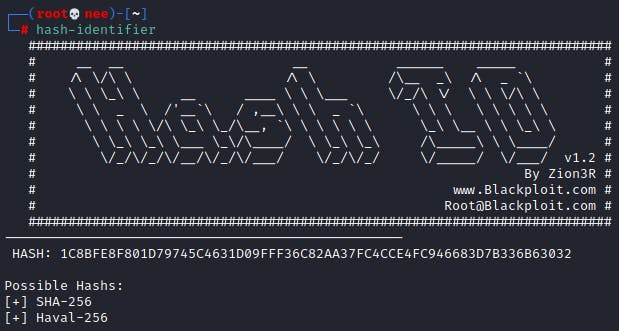
Hashcat
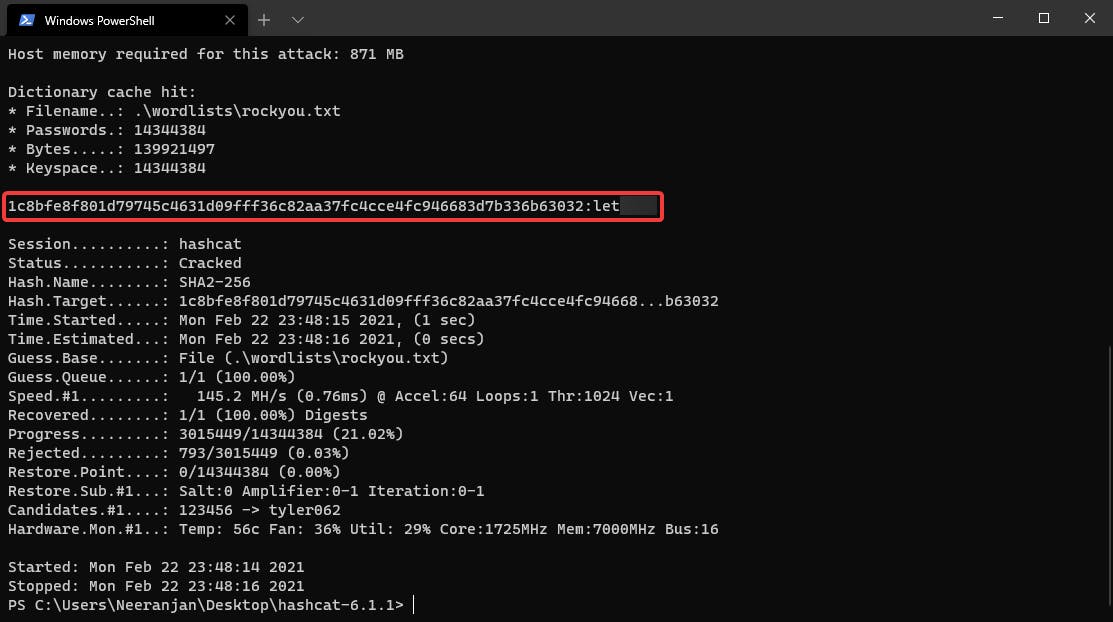
.\hashcat.exe -m 1400 .\hashes\hash.txt .\wordlists\rockyou.txt -O --force
1.4 ~ Bcrypt
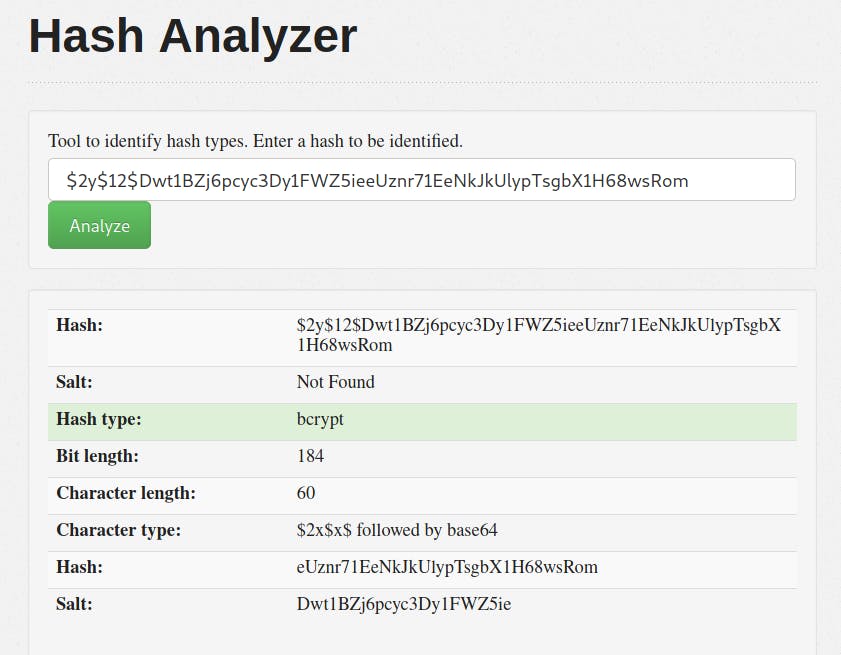
For this one, Hash-Identifier was not able to detect the type of hash. Thus, I used an online tool named Hash Analyzer.
$2y$12$Dwt1BZj6pcyc3Dy1FWZ5ieeUznr71EeNkJkUlypTsgbX1H68wsRom : Bcrypt
Hash Analyzer
Hashcat
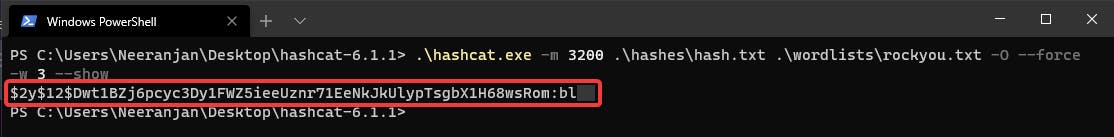
.\hashcat.exe -m 3200 .\hashes\hash.txt .\wordlists\rockyou.txt -O --force
Cracking Bcrypt usually takes about 10-15 hours; Cracked Password = bleh
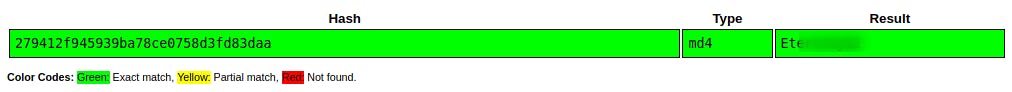
1.5 ~ MD4
279412f945939ba78ce0758d3fd83daa : MD4
Hash Identifier
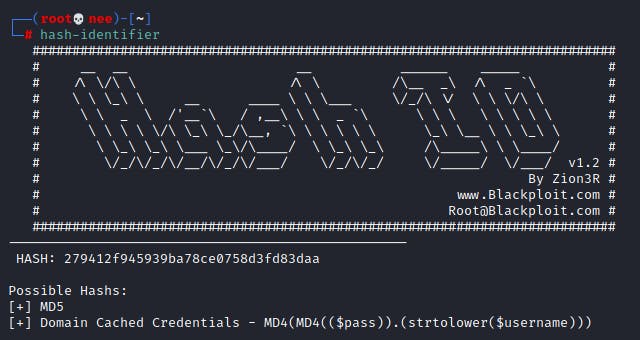
Hashcat
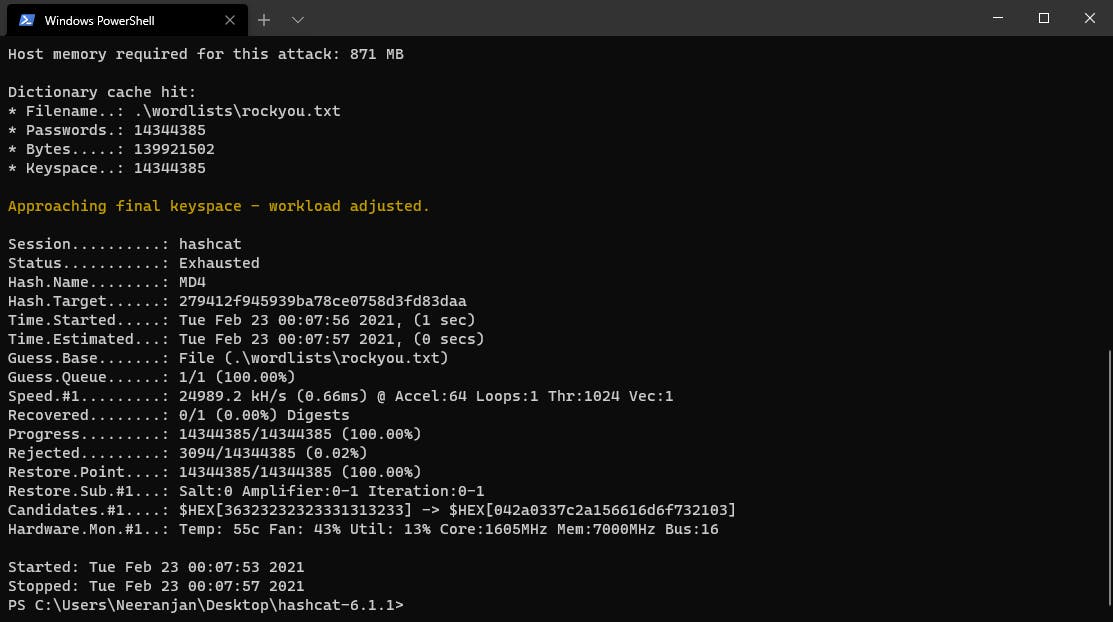
.\hashcat.exe -m 900 .\hashes\hash.txt .\wordlists\rockyou.txt -O --force
The password for this task actually doesn't exist in the RockYou.txt wordlist. Thus, I decided to use an online cracker for this task.
Task 2
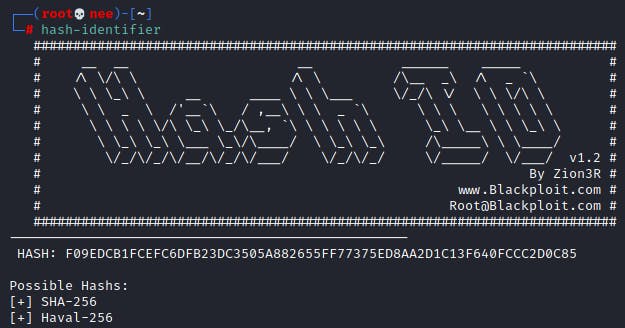
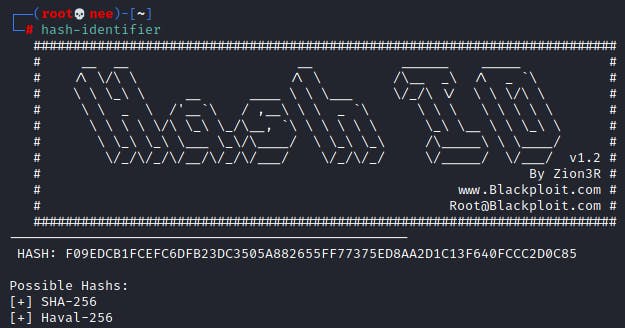
2.1 ~ SHA-256
F09EDCB1FCEFC6DFB23DC3505A882655FF77375ED8AA2D1C13F640FCCC2D0C85 : SHA-256
Hash Identifier
Hashcat
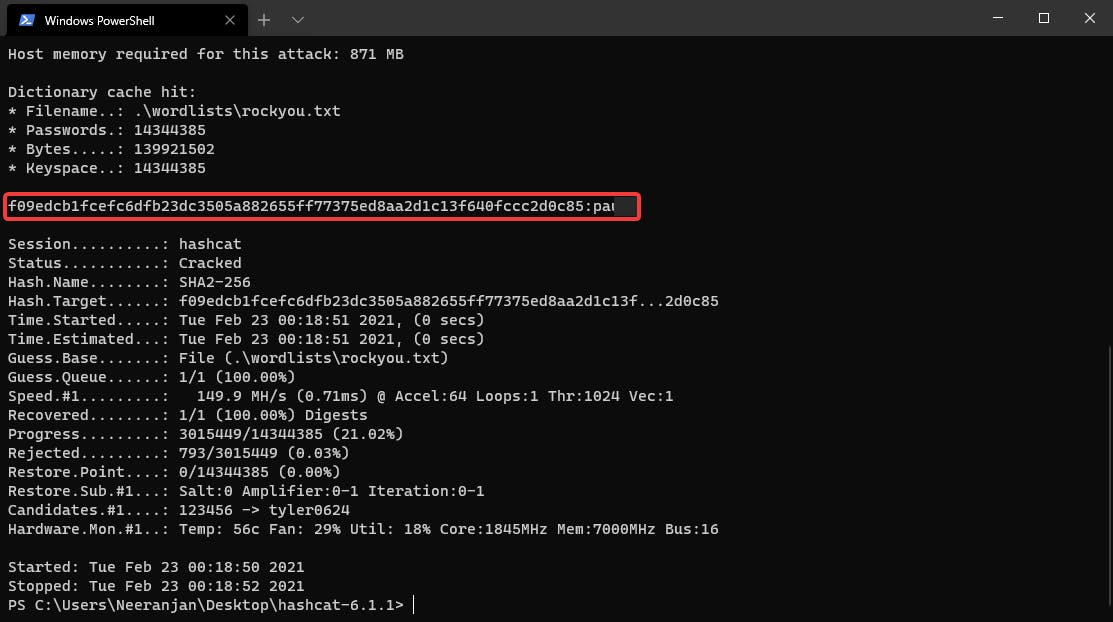
.\hashcat.exe -m 1400 .\hashes\hash.txt .\wordlists\rockyou.txt -O --force
This task was the exact same as 1.3.
2.1 ~ SHA-256
F09EDCB1FCEFC6DFB23DC3505A882655FF77375ED8AA2D1C13F640FCCC2D0C85 : SHA-256
Hash Identifier
Hashcat
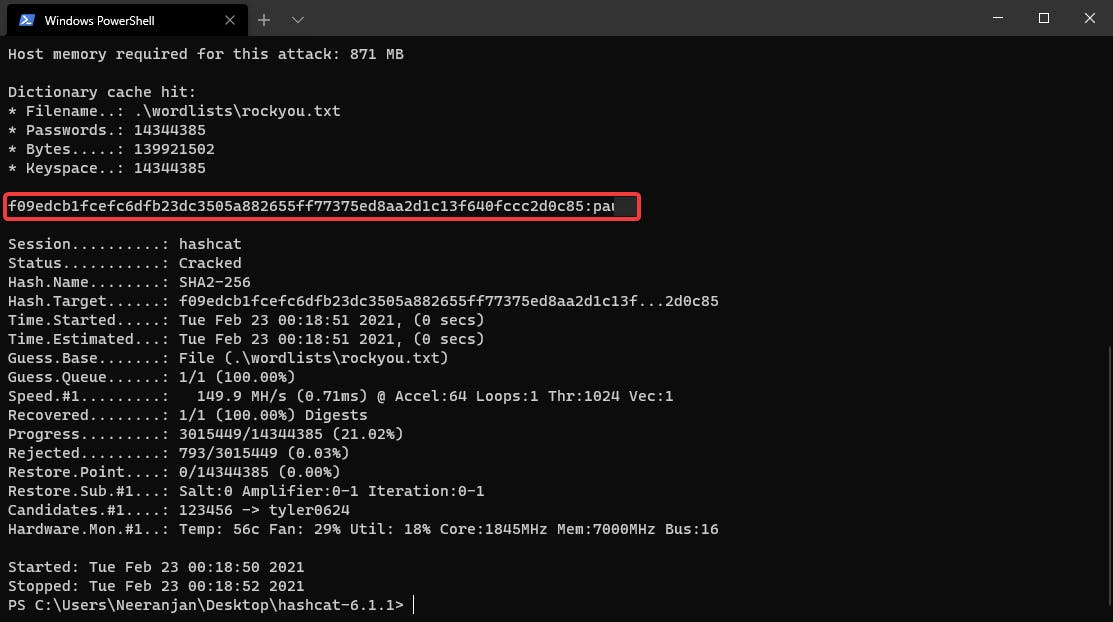
.\hashcat.exe -m 1400 .\hashes\hash.txt .\wordlists\rockyou.txt -O --force
This task was the exact same as 1.3.
2.2 ~ NTLM
1DFECA0C002AE40B8619ECF94819CC1B : NTLM
Hash Identifier
Hash Identifier actually falsely identified the hash as MD4/MD4. I then went by the possible hashes to find out that it was NTLM.
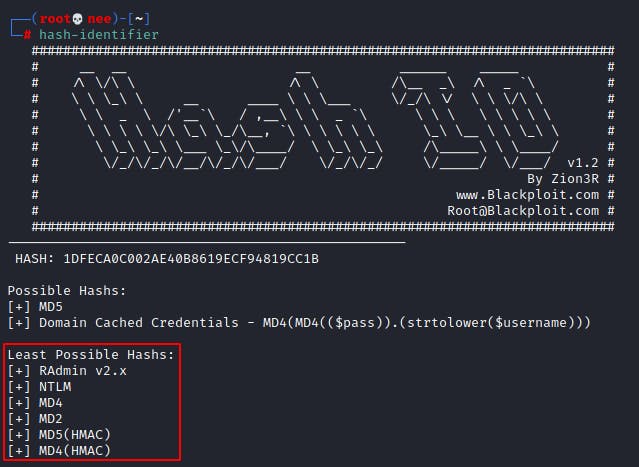
Hashcat
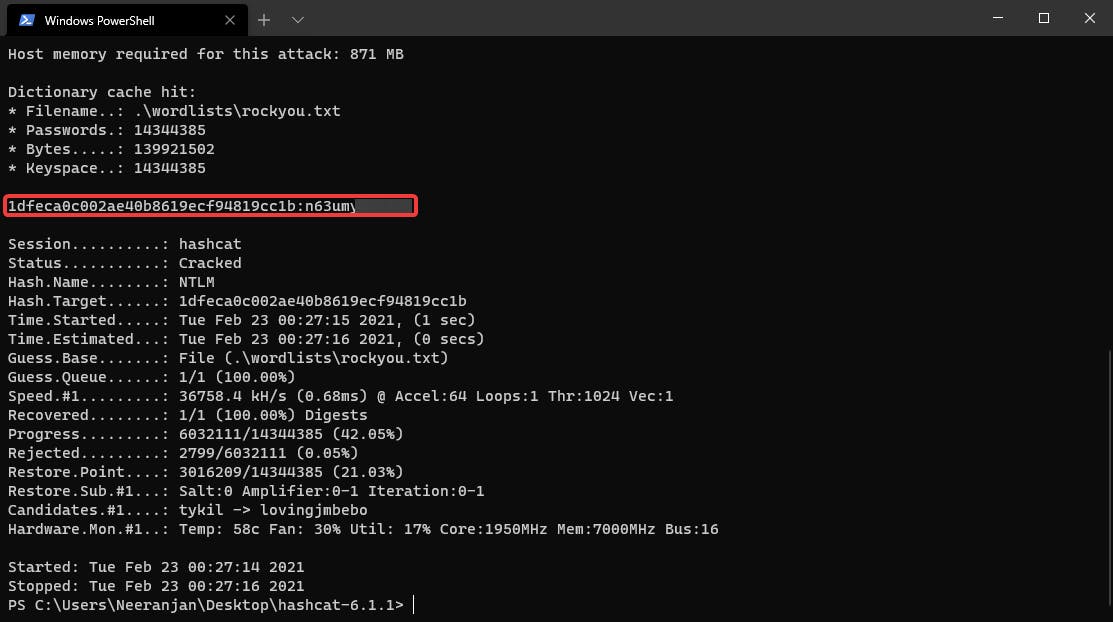
.\hashcat.exe -m 1000 .\hashes\hash.txt .\wordlists\rockyou.txt -O --force
2.3 ~ sha512crypt
$6$aReallyHardSalt$6WKUTqzq.UQQmrm0p/T7MPpMbGNnzXPMAXi4bJMl9be.cfi3/qxIf.hsGpS41BqMhSrHVXgMpdjS6xeKZAs02. : sha512crypt
Hash Identification
Hash Identifier was not able to identify this hash. Thus, I set out to find an online identifier which was able to identify the has type. That's when I landed on [suIP.biz](https://suip.biz/?act=hashtag)'s hash identifier. It was not only able to identify the hash type, but it also gave me the hashcat mode to use.
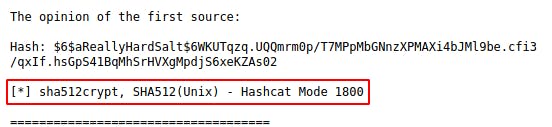
Hashcat
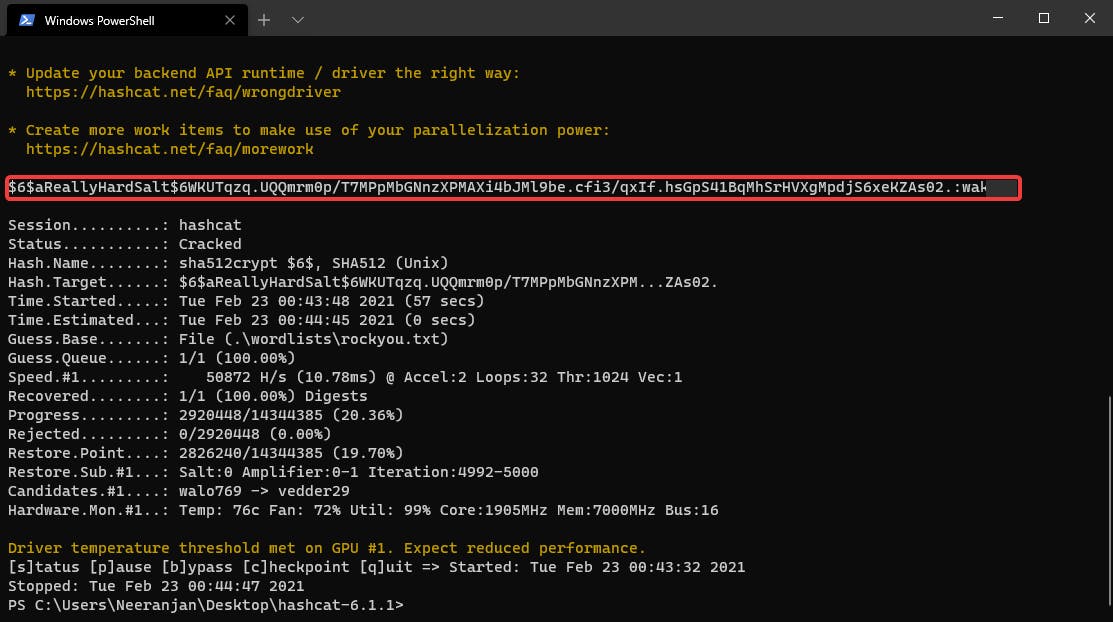
.\hashcat.exe -m 1800 .\hashes\hash.txt .\wordlists\rockyou.txt
2.4 ~ SHA1
e5d8870e5bdd26602cab8dbe07a942c8669e56d6:tryhackme : SHA1
Hash Identification
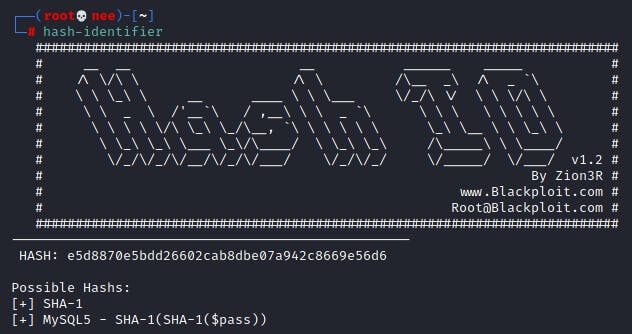
Hashcat
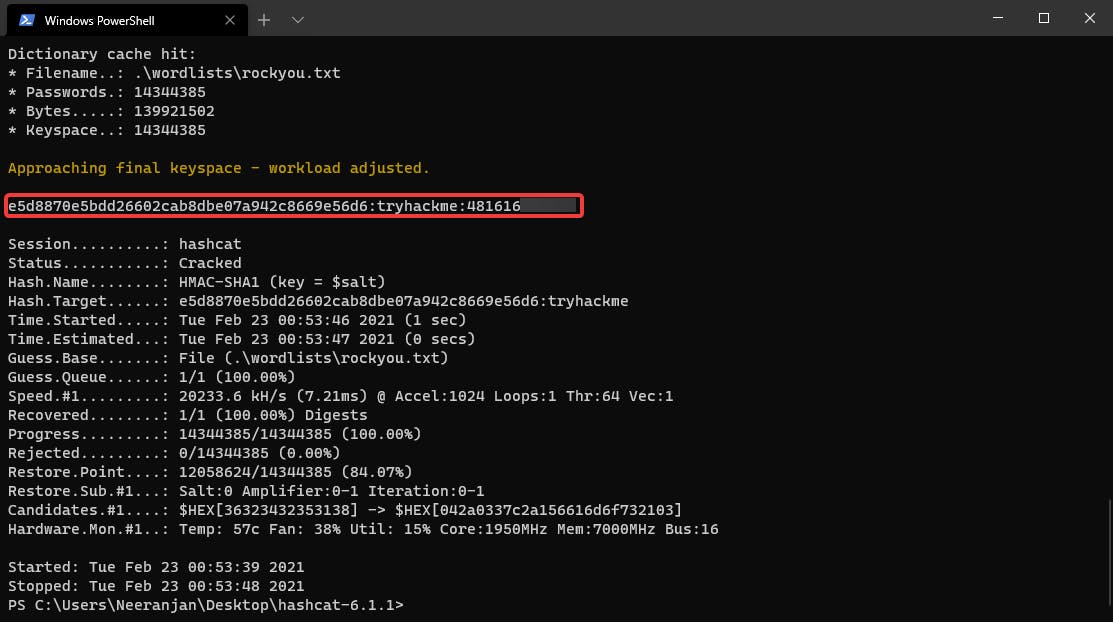
.\hashcat.exe -m 160 .\hashes\hash.txt .\wordlists\rockyou.txt
Interesting challenge! Was able to learn so much about cracking and the types of hashes!